Payment fraud does not depend on the availability of instant payments in order to work. However, by removing the time lag between initiation and settlement, instant payment makes these frauds all but impossible to block once the payment has been made. The cash will leave the victim’s account almost immediately and be available in the fraudster’s account mere seconds later.
In the UK, annual losses from online banking fraud almost tripled in the 18 months after the UK’s Faster Payments system went live at the end of May 2008. Fraud losses climbed from £22.6m ($27.5m) in 2007 to £52.5m ($63.9m) in 2008 and £59.7m ($72.6m) a year later, and banks struggle to strengthen their internal defenses. By 2018, the first year in which UK Finance published figures, losses from so-called authorized push payment fraud had reached £236m ($287m).
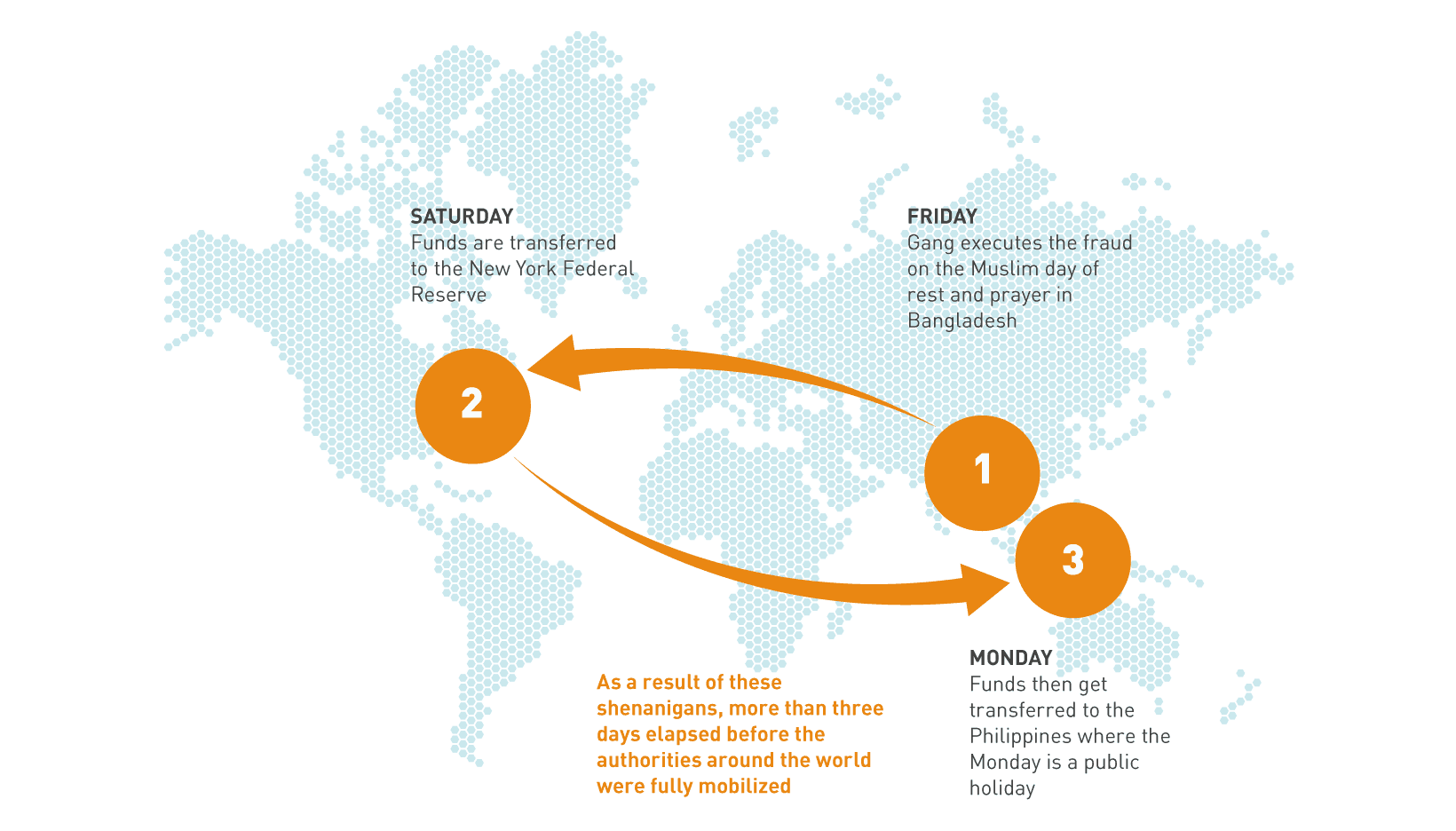
International payments also open up timing opportunities for fraudsters. For example, in the case of the theft from the Bangladesh Central Bank, using the SWIFT network, the gang executed the fraud on a Friday – the Muslim day of rest and prayer in Bangladesh – which was followed by the weekend in the US, where the funds were held at the New York Federal Reserve before their transfer to the Philippines, where the following Monday was a public holiday. As a result, more than three days elapsed before the authorities around the world were fully mobilized. To date, of $101m fraudulently transferred from the New York Federal Reserve, $81m remains unaccounted for.
Equally, a fraudulent international e-commerce payment made on a Friday evening will move from the e-banking system to the core banking platform and then be transferred a few hours later to the SWIFT system to complete the cross-border payment. By the following Monday, the
funds have reached the fraudster’s account.
This highlights the dual nature of the challenge that payment fraud poses to banks in the era of instant payments. Detecting and blocking these fraudulent payments not only represents a major technology challenge for them, but it also exposes operational weaknesses in organizations that do not have teams in place to monitor and validate instant payments round the clock and through weekends.